Every serious conversation about decentralized AI eventually arrives at the same realization: moving data at scale is expensive, centralized, and controlled by a very small number of companies.
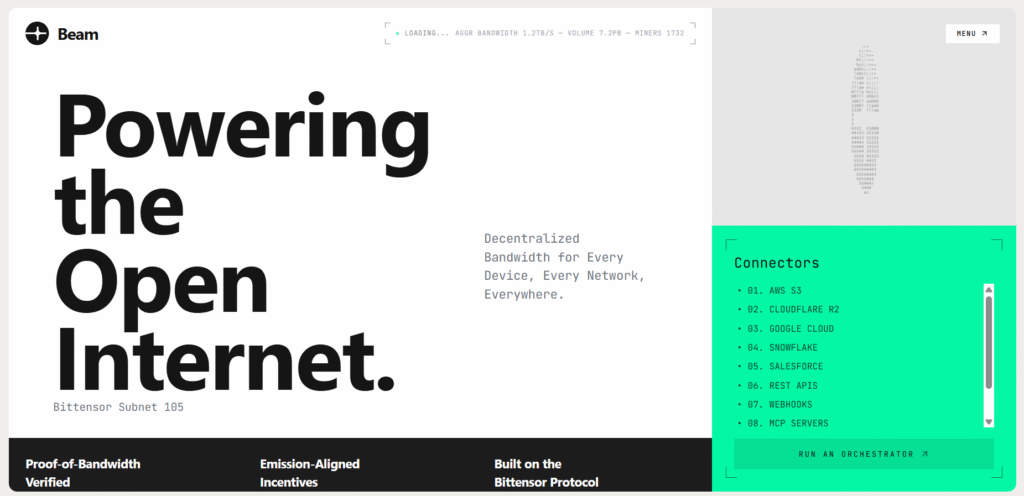
Storage has Hippius, compute have Lium and Targon, but bandwidth, the actual infrastructure for moving enormous volumes of data between machines, has had no serious decentralized answer. Nic Savy noticed that gap, and built Beam.
What Beam (Subnet 105) Actually Is
Mark opened simply: “Tell me about Beam. What is Subnet 105 and what are you guys doing?”
Nic’s answer was direct. “Beam is our attempt to create a distributed bandwidth network on top of Bittensor. I noticed there was a gap when it comes to bandwidth, so we decided to see what we can do.” Mark connected it immediately: “If you want to move a giant amount of data, you need a giant amount of bandwidth, and that’s very expensive once you get to large amounts. And it just turns out AI uses large amounts of data.”
Nic pushed it further. “Because of AI, bandwidth will become a more valuable commodity. You need to move data back and forth with all the agents who will be on the market. So let’s find a way to utilize what we have and move data faster.”
The way Beam moves that data is built around security and resilience from the ground up:
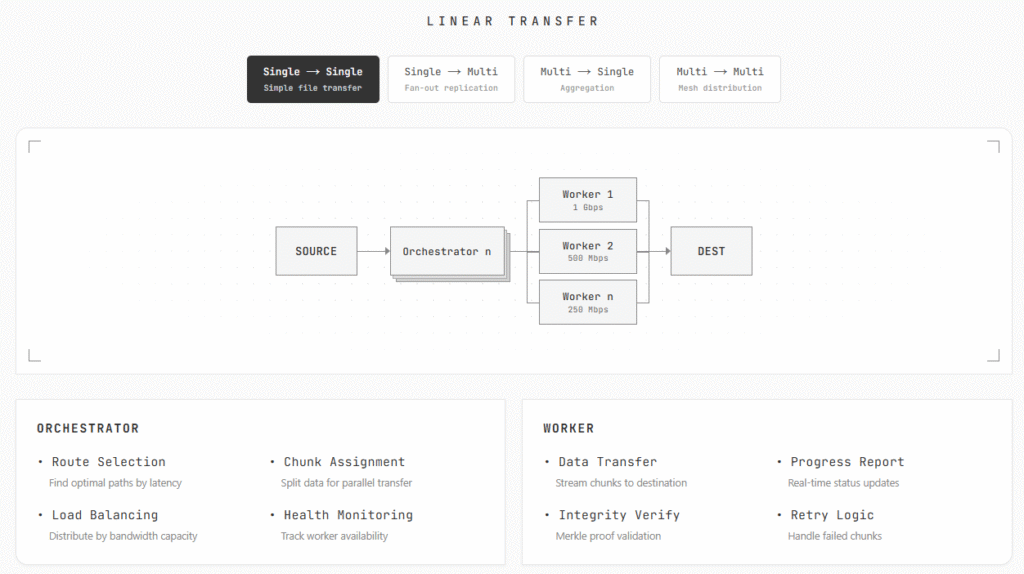
a. Files are broken into small encrypted chunks of five to ten megabytes each,
b. Those chunks are distributed across a network of miners, called orchestrators, who use their bandwidth to move pieces toward the destination,
c. A robust retry mechanism handles failures automatically since miners are unknown participants, and
d. At the destination, chunks are reassembled and decrypted, never readable by anyone who handled them in transit.
Mark made the security point explicit: “While it’s in transit, it’s encrypted. Even if I intercept it, I can’t see it.” Nic confirmed: “Exactly. That’s super important.”
In a recent live test, Beam moved 500 megabytes across a distributed network of unknown nodes in 21 to 29 seconds, comparable to transfers between major cloud providers over the public internet.
The Market They Are Going After
Nic spent two decades as an enterprise architect working with Fortune 100 companies on exactly the data migration problems Beam is built to solve. Mark asked directly: “If you didn’t exist and I had need of your services, who do I go to right now?”
Nic laid it out. “Today, companies either build in-house infrastructure, which means spending a lot of money on servers and support teams, or they partner with an ETL (Extract, Transform, Load) company like Informatica. We are talking about millions of dollars per device in licenses.”
Beam replaces both with a dynamic, on-demand pipeline:
a. No long-term licensing contracts or dedicated infrastructure to maintain,
b. Enterprises open a pipeline when they need it and close it when they are done, and
c. Cost expected to be dramatically lower than centralized alternatives.
Mark put a number on it the way only he would: “It’s the law of nature I’ve seen in Bittensor. Typically it’s like one-tenth the cost.” Nic smiled: “The cost will be drastic.”
The Compliance Tier Nobody Expected
One of the more unexpected parts of the conversation was Beam’s two-tier miner structure. Mark caught it immediately: “There is a class of miner in your system that will be SOC 2 and HIPAA compliant?” Nic: “And more.”
The two tiers work as follows:
a. Certified Tier: Orchestrators who pass SOC 2, HIPAA, and additional compliance checks, forming private bandwidth pools for regulated enterprise clients who need full accountability, and
b. Open Tier: Permissionless participation for developers and startups who need fast, affordable data transfer without compliance overhead.
“As a corporation,” Nic explained, “clients need to know that these are real companies and real providers. So we will have certified providers for enterprise clients, and then the network remains open for everyone else.”
The Anti-Dump Mechanic Mark Had Never Heard Before
The conversation took an unexpected turn when Nic introduced an incentive idea that stopped Mark mid-sentence. “We are looking at the $TAO outflow from each miner,” Nic said. “If the goal is to mine and just extract value, we don’t want that.”
Mark’s reaction was immediate: “You get punished for dumping. I’ve never heard anybody come up with that.” He pushed further: “The corollary is also reward. If you hold the token longer, the network favors you. That’s a great idea.” Nic kept it simple: “Quality of bandwidth is the most important thing. That’s what we will be focusing on.”
Beam and the Agent Economy
Mark raised the question of AI agents as future customers: “B2C is no longer business to consumer, it’s business to agent. But the agent needs to be made aware of your existence. How do you think about marketing to Claude?”
Nic was ready. “Our stack is already compatible with Claude. We have not yet published the skill, but it is compatible.” Mark clarified: “You are going to publish a how-to-use-me skill specifically made for agents, teaching them how to use Beam and how to pay you.” Nic confirmed: “Exactly.”
One layer of accountability applies regardless of who is making the request. Every API key requires registration, linking usage to a real entity. “In order to get an API key from Beam, you need to register,” Nic said. Mark put it plainly: “You’ve got to know who the person behind the agent is.” Nic: “Exactly.”
What Is Coming Next
Nic closed with a clear picture of what is ahead:
a. A client portal for enterprise onboarding, expected within roughly a month,
b. A published vibe miner guide to lower the barrier for anyone wanting to mine without a machine learning background, and
c. Further decentralization of the orchestration mechanism, eventually moving coordination logic fully on-chain.
Beam is backed by Yuma, following an introduction through Max Sebti of Score, and is a few weeks into mainnet operation at the time of recording.
Conclusion
Mark closed the show with his honest read on the product: “The bulk of your customers probably don’t care that it’s Bittensor. They’re just like, it’s SOC compliant, HIPAA compliant, and a tenth of the cost. So I use this. And I think this could be enormous.”
Nic Savy spent twenty years solving enterprise data problems from the inside, and Beam is the product that experience was always pointing toward. The compliance tier, the anti-dump incentive design, and the agent-compatible stack all reflect a builder who understands what it takes to earn the trust of institutions that have never touched a blockchain and never plan to. The infrastructure is being laid, and the market it is going after is very large and very ready.
Watch the full Hash Rate episode below:
Enjoyed this article? Join our newsletter
Get the latest TAO & Bittensor news straight to your inbox.
We respect your privacy. Unsubscribe anytime.



Be the first to comment