
Decentralized compute have struggled to move beyond cost efficiency into enterprise-grade adoption due to one core limitation, which is trust. Most networks expose workloads to machine operators, making them unsuitable for sensitive data and high-value use cases.
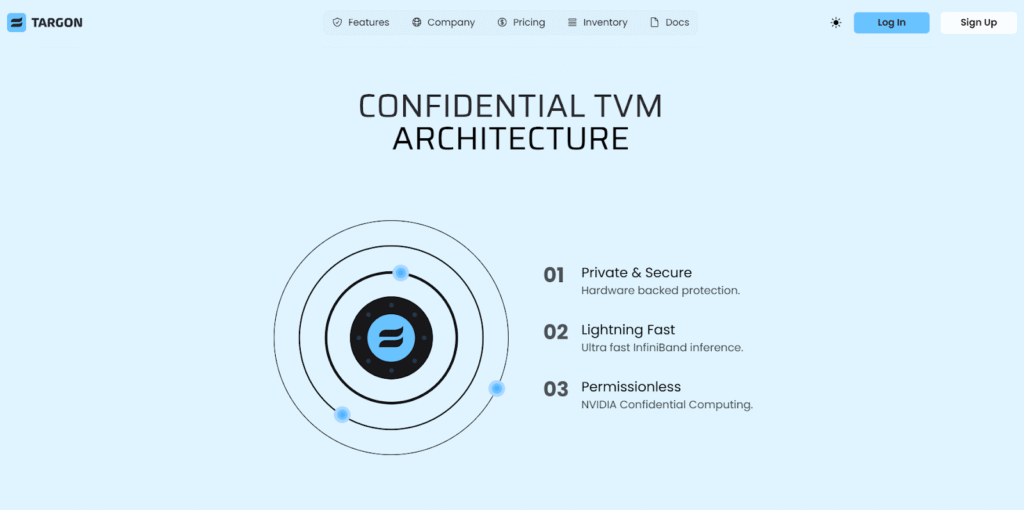
While Targon Virtual Machine (TVM) addressed this with hardware-backed security, it also restricted participation to a narrow class of infrastructure. TargonOS extends secure compute to a much broader hardware base, introducing a more flexible trust model that enables scale without abandoning practical security guarantees.
What TargonOS Introduces
TargonOS is a purpose-built operating system that transforms general-purpose machines into fully managed nodes within the Targon (Bittensor Subnet 4) network. Instead of complex setup processes:
a. Operators install a single system image,
b. Initialize it, and
c. The machine becomes active with minimal ongoing involvement.
Once deployed, the system operates in a locked, self-managed state, and updates are handled automatically, failures revert safely, and operator access to the execution layer is removed. This ensures consistency across nodes while reducing the risk of interference.
For users, TargonOS shifts the experience from constrained execution environments to fully isolated virtual machines. Each workload runs in its own encrypted environment with full control over software, dependencies, and configuration, bringing decentralized compute closer to the expectations set by traditional cloud infrastructure.
Unlocking a Broader Supply of Compute
Earlier approaches relied on specialized hardware to guarantee strong security, which limited the number of machines that could participate. TargonOS introduces a different model that works with widely available systems, allowing a significantly larger portion of global compute to join the network.
This expansion unlocks a vast pool of underutilized GPUs (Graphics Processing Unit) and general-purpose machines that were previously excluded. As supply increases, pricing becomes more competitive, and operators gain new opportunities to monetize idle hardware. This is a more efficient and accessible to a compute market that better reflects real-world availability.
From Restricted Environments to Full Control
One of the key limitations of earlier systems was the reliance on containerized workloads. While efficient, containers do not provide the level of control required for more complex use cases such as custom training pipelines or multi-node coordination.
TargonOS replaces this limitation with full virtual machines. Users gain root-level access within isolated environments, enabling them to configure and run any software stack they require. Dedicated hardware access further enhances this flexibility, allowing workloads to fully utilize available resources without abstraction constraints.
This shift removes a major barrier to adoption by aligning decentralized compute with the operational needs of advanced users and teams.
Simplifying Participation for Operators
Operational complexity has historically limited who can participate in decentralized networks, and systems that require deep technical expertise tend to concentrate control among a small group of operators.
TargonOS reduces this friction by abstracting away nearly all operational responsibility. The system installs once, manages itself, and requires no manual maintenance. Operators are not responsible for configuration, updates, or workload management, their role is limited to maintaining uptime, while the protocol handles everything else.
This approach broadens participation while ensuring uniform behavior across the network, strengthening both decentralization and reliability.
A Practical Approach to Security
Without relying on specialized hardware for full memory encryption, TargonOS adopts a layered security model built on cryptographic guarantees and system integrity checks. The system verifies its state during boot using hardware-backed attestation before allowing access to encrypted resources.
Data remains protected through disk-level encryption and remote key management, ensuring that sensitive information cannot be accessed directly from the host machine. Each user environment is independently secured, preventing cross-access and maintaining isolation across workloads
While this model does not match the absolute guarantees of hardware-enforced isolation, it provides a strong and practical level of security suitable for a wide range of applications.
A Dual-Tier Compute Network
With TargonOS, the network evolves into a dual-tier system that balances security and scale. High-assurance environments continue to operate on specialized infrastructure for workloads that require maximum protection. Alongside this, a broader tier of community-powered nodes provides flexible and cost-efficient compute for less sensitive use cases.
Users interact with both tiers through a unified interface, selecting the appropriate environment based on their needs without added complexity. This structure allows the network to serve a wider range of workloads while maintaining clear trust boundaries.
Toward a Sustainable Compute Economy
TargonOS expands decentralized compute beyond its previous limitations by aligning accessibility, flexibility, and security within a single framework. By unlocking a larger supply of hardware and enabling more practical workloads, it strengthens the foundation for sustained demand rather than experimental usage.
This shift moves the network closer to a model where compute is not only decentralized, but also economically viable at scale.
Enjoyed this article? Join our newsletter
Get the latest Bittensor & TAO ecosystem news straight to your inbox.
We respect your privacy. Unsubscribe anytime.



Be the first to comment